According
to Professor
Raina McIntyre (Global Biosecurity, Head of Biosecurity
Program, Kirby Institute UNSW New South Wales) on 2 April 2022,
COVID-19 case numbers are bouncing around. Case numbers in
New South Wales have increased since a low of 4,916 daily cases on 21
February 2022. “In the past week, they have ranged from
17,000 to more than 25,000 a day”.
“Part
of the problem is the lack of testing and the lack of reporting. The
message of “live with it” runs counter to the importance of
reporting a positive test, if you can afford one. PCR testing remains
restricted, so daily case numbers are a substantial underestimate and
even the trends may not be accurate.” [my yellow highlighting]
As
of 4pm 1 April 2022 there were 20,389 new confirmed cases
of COVID-19 in New South Wales and a total of 268,761
active COVID-19 cases across the state the majority of
which are being self-managed at home.
There
were 1,302 COVID-19 cases admitted to hospital as at 4pm 1
April, including 47 people in intensive care, 16 of whom require
ventilation.
NSW
Health reported the deaths of 13 people with COVID-19 –
seven women and six men. Of these, 7 people were aged in their 70s, 5
people were aged in their 80s and 1 person was aged in their 90s.
Included
in the day’s total of newly confirmed COVID-19 cases were 520
people in Northern NSW.
There
were 14 COVID-19 cases admitted to hospital with 2 in
intensive care.
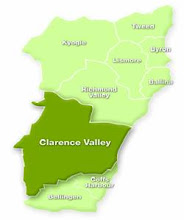
These
520 cases were all 7 local government areas within Northern
NSW:
Tweed
Shire – 149 cases across
postcodes 2483,
2484, 2485,
Lismore
City – 82 cases across
postcodes 2472,
2480;
Clarence
Valley – 79 cases across
postcodes 2460,
2462,
2453, 2464,
2466;
Ballina
Shire – 75 cases across
postcodes
Byron
Shire – 73 cases across
postcodes 2479,
2481, 2482, 2483,
Richmond
Valley – 51 cases across
postcodes 2469,
2470, 2471, 2473;
Kyogle
Shire – 11 cases across
postcode 2474;
TOTAL
520
According
to the federal Dept. of Health as of 31 March 2022
there were 229
COVID-19 outbreaks in residential aged care facilities involving 976
residents.
A
full list of these NSW facilities can be found at
https://www.health.gov.au/sites/default/files/documents/2022/04/covid-19-outbreaks-in-australian-residential-aged-care-facilities-1-april-2022_0.pdf
On
10 February 2022, the Australian Government announced changes to
the definition of fully vaccinated against COVID-19 so as to
include vaccine booster doses required for those 16 years and over.
The new term in use is “up to date” vaccination.
Therefore
as of 1 April 2022
only 60.2% of people aged 16 years to 90 years and older, 79.5% of
children aged 12 to 15 years and 26.9% of children aged 5 to 11 years
are considered to be “up to date” (fully vaccinated).
The fact that New South Wales is falling behind recommended vaccination rates is a concern given this statement.
ATAGI
Statement,
26 March 2022:
ATAGI
recommends an additional booster dose of COVID-19 vaccine to increase
vaccine protection before winter for selected population groups (see
Table 1) who are at greatest risk of severe illness from COVID-19 and
who have received their primary vaccination and first booster dose.
These groups are:
- Adults
aged 65 years and older
- Residents
of aged care or disability care facilities
- People
aged 16 years and older with severe immunocompromise (as defined in
the ATAGI statement on the use of a 3rd primary dose of COVID-19
vaccine in individuals who are severely immunocompromised)
- Aboriginal
and Torres Strait Islander people aged 50 years and older.
The
additional winter booster dose can be given from 4 months or longer
after the person has received their first booster dose, or from 4
months after a confirmed SARS-CoV-2 infection, if infection occurred
since the person’s first COVID-19 booster dose.
ATAGI
recommends that the rollout of the additional booster dose for these
groups starts from April 2022, coinciding with the rollout of the
2022 influenza vaccination program.
As
of 4pm 2 April 2022 there were 16,807 new
confirmed cases of COVID-19 in New South Wales and a total of ?
active COVID-19 cases across the state the majority of which are
being self-managed at home.
There
were 1,355
COVID-19 cases admitted to hospital
as at 4pm 2
April, including 50
people in intensive care, 19
of whom require ventilation.
NSW
Health reported the deaths of 11 people with
COVID-19 – seven women and four men. Of these, 1 person was
aged in their 30s, 1 person was in their 50s, 1 person was in their
70s, 6 people were in their 80s and 2 people were in their 90s.
Included
in the day’s total of newly confirmed COVID-19 cases were 471
people in Northern NSW.
There
were 14 COVID-19 cases admitted to hospital with 1 in
intensive care.
These
471 cases were all 7 local government areas within Northern NSW:
Tweed
Shire – 144 cases across
postcodes 2484,
2484, 2486, 2487, 2488, 2489;
Clarence
Valley – 75 cases across
postcodes 2460,
2462, 2462, 2464,
2465;
Byron
Shire – 71 cases across
postcodes 2479,
2481, 2482, 2483;
Lismore
City – 67 cases across
postcodes
Ballina
Shire – 66 cases across
postcodes 2478,
2479;
Richmond
Valley – 41 cases across
postcodes 2469,
2470, 2471, 2472, 2473;
Kyogle
Shire – 5 cases across
postcode 2474;
Tenterfield
Shire – 2 cases across
postcode 2476;
Tenterfield
is not in the NNSWLHD but shares a postcode so some cases are
included here.
TOTAL
471
On
deaths in Australia…..
At
the tail end of the Delta wave in December 2021, where we could
reasonably point to the start of the Omicron wave, we had 2006
deaths. The Omicron wave saw close to a 200 per cent increase in
deaths compared with all previous waves combined, with 5928 deaths by
March 29. This includes six deaths in children under 10, two in
people aged 10-19 years, 16 in the group 20-29 and 52 deaths in
people 30-39 years old. The largest single age group for deaths was
in people 80-89 years, with 2025 deaths. Another 2100 or so deaths
were recorded in people aged 40-79 years and the remainder – about
1400 deaths – in people aged 90 years and over. [Professor
Raina McIntyre writing in The
Saturday Paper,
2 April 2022]
As
of 4pm 3 April 2022 there were 15,572 new
confirmed cases of COVID-19 in New South Wales and a total of
266,110 active COVID-19 cases across the state the majority of
which are being self-managed at home.
There
were 1,418 COVID-19 cases admitted to hospital as at 4pm 3
April, including 56 people in intensive care, 18 of whom require
ventilation.
NSW
Health reported the deaths
of 6
people with COVID-19 –
four
women and two
men. Of these, 1
person was aged in their 70s, 3
people were in their 80s and 2
people were in their 90s.
Included
in the day’s total of newly confirmed COVID-19 cases were 437
people in Northern NSW.
There
were 19 COVID-19 cases admitted to hospital with 1 in intensive care.
These
437 cases were all 7 local government areas within Northern NSW:
Tweed
Shire – 113 cases across postcodes 2483, 2484, 2486, 2486,
2487, 2488, 2489;
Ballina
Shire – 83 cases across postcodes 2477, 2478;
Byron
Shire – 69 cases across postcodes 2479, 2481, 2482, 2483;
Clarence
Valley – 62 cases across postcodes 2460, 2463, 2464;
Lismore
City – 55 cases across postcode 2479;
Richmond
Valley – 43 cases across postcodes 2469, 2479, 2471, 2472,
2473;
Kyogle
Shire – 12 cases across postcode 2474.
TOTAL
437
A reminder......
NSW
Health states:
Everyone
is urged to take simple precautions to protect each other from
COVID-19, such as:
use
a mask in indoor settings where you cannot maintain a safe physical
distance from others
get
your booster vaccine
get
a test and isolate immediately if you have any COVID symptoms
clean
your hands regularly.
SOURCES:
https://www.health.nsw.gov.au/news/Pages/2022-nsw-health.aspx
https://www.health.nsw.gov.au/Infectious/covid-19/Pages/stats-nsw.aspx#today
https://www.health.gov.au/health-alerts/covid-19
BACKGROUND
Current
SARS-C0V-2 Variants of Concern in Australia
B.1.617.2
(Delta) and sub-lineages AY.*
B.1.1.529
(Omicron) and sub-lineages BA.*
SARS-CoV-2
Variants Which Decided To Call Australia Home
SARS-CoV-2
Variant A.2.2, Identified 2020-03-17, Australian lineage.
Australia
92.0%, New_Zealand 2.0%, Canada 2.0%, United States of America 2.0%,
United Kingdom 1.0%.
SARS-CoV-2
Variant D.2, Identified 2020-03-19, Alias of B.1.1.25.2,
Australia.
Australia
100.0%, United States of America 0.0%, Chile 0.0%, Mexico 0.0%,
United Kingdom 0.0%.
SARS-CoV-2
Variant D.3, Identified 2020-06-14, Alias of B.1.1.25.3,
Australia.
Australia
100.0%.
SARS-CoV-2
Variant B.1.1.136, Identified 2020-06-03, Australian lineage.
Australia
86.0%, Turkey 7.0%, Russia 5.0%, United Kingdom 2.0%.
SARS-CoV-2
Variant B.1.1.142, Identified 2020-03-03, Australian lineage.
Australia
39.0%, United Kingdom 12.0%, Iceland 12.0%, Switzerland 6.0%, United
States of America 6.0%.
___________________________